A major security incident can negatively impact an organization with unending consequences. It could lead to loss of valuable customers, reputational damage, drop in revenue, or loss of intellectual properties.
While large enterprises can still weather through the impact of the data breach, it could be the end for a startup. In this article we share insight on how to create an incident response plan template (or IR plan in short).
- What is an incident response plan for a startup?
- The SANS Institute's 6 Steps of Incident Response
- Incident Response Plan Template - SM (Small)
- Incident Response Plan Template - MD (Medium)
- Incident Response Plan Template - LG (Large)
- Incident handling and reporting procedures
- Runbooks - Practice, Practice, Practice
- Summary
What is an incident response plan for a startup?
An incident response plan or IR plan is a set of tools and processes startups can leverage to detect, eliminate and recover from cyber threats. The goal of the IR plan is to help the security team respond proactively and uniformly.
However, it is not enough to respond, but responses must be effective. An incident response plan ensures startups minimize the impact of threats, data breaches, abuse of intellectual properties, and loss of customer loyalty on their business operations.
The SANS Institute's 6 Steps of Incident Response
The Incident Handlers Handbook by the SANS Institute highlighted six steps startups' security teams can apply to manage security incidents. Your incident response plan template should be structured to accommodate the following steps:
Preparation
- Review and codify your startup security policy.
- Perform a risk assessment
- Identify your confidential and sensitive assets.
- Define critical incidents your security team should prioritize.
- Set Up an Incident Response Team.
Identification
- Monitor and detect anomalies in your IT systems.
- contrary to your normal operations and procedures.
- Check if those anomalies or deviations qualify as major security incidents.
- If you discover incidents, source for additional evidence, confirm its type and severity.
- Then, document your findings.
Containment
- Implement short-term containment such as isolating the attack vector or compromised network or systems.
- Prioritize long-term containment to include temporary fixes to ensure the 24/7 running of systems and networks while you rebuild a clean system and network.
Eradication
- Eliminate viruses and malware from all systems and networks.
- Find out the root cause of the threat.
- Establish proactive actions to exterminate similar threats in the future.
- If the threat is caused by weak authentication, patch with strong authentication.
Recovery
- Restore all affected and patched systems online.
- Test, verify, and monitor to ensure that those systems and networks are working optimally.
Lessons Learned
- Perform a retrospective session not later than two weeks from when the incidents occur.
- Document the entire incident, investigate the security incident further, appraise what was done during containment, and understand if the process can be improved in the future when an incident occurs.
Incident Response Plan Template - SM (Small)
No startup won't experience security incidents in its business life cycles. There could be business email compromise, phishing attacks, ransomware, or data breach.
You can use Incident Response Plan template prepared by Ryan McGeehan on GitHub. It is intended to be fairly minimal to get a team started without a significant amount of effort.
You can easily pin this template in your Slack or somewhere in your company's wiki where responders can easily see it.
Any of your employees can discover and sound an alarm about an incident. Thus, you need to create a familiar spot for reporting such issues. It could be a dedicated email, a Slack bot, slack channel, or mobile phone. Just ensure it is reliable and socialized.
Your employees must be well informed on how severe or less severe an incident is and when to request external intervention or resources.
- Critical Severity - incident with a great impact. i.e a security breach, data loss, or support service downtime. Critical issues include active exploitation by malicious actors. Get the executive leaders involved at this stage, notify the CEO, CTO, and COO. Do not stop escalating until the message is acknowledged.
High Severity - incident with a significant effect. For instance, support system downtime for some customers. Only treat a high or critical severity after investigation or confirmation. This level of severity should keep the incident responders on their toes. You can tag a message to emergency@company.com with 'Urgent' in the subject line.
Low and Medium Severity - a minor event with low impact. A system glitch causing a slight discomfort for customers.
Incident Response Plan Template - MD (Medium)
A good cyber incident response plan helps organisations to get their response right. UK security consultancy Cydea, brands itself as an optimistic cyber security consultancy believes that good cyber security:
- starts with a deep and thorough understanding of how your organisation works
- provides the strongest protection for the most important things
Due to lack of a decent IR plan template to start from, they set about researching, distilling and compiling all the best practice, augmented from our experience responding to some of the highest-profile cyber events in recent years.
**This template is simple to apply, just download template IR Plan Template, or a copy of the Google Docs version
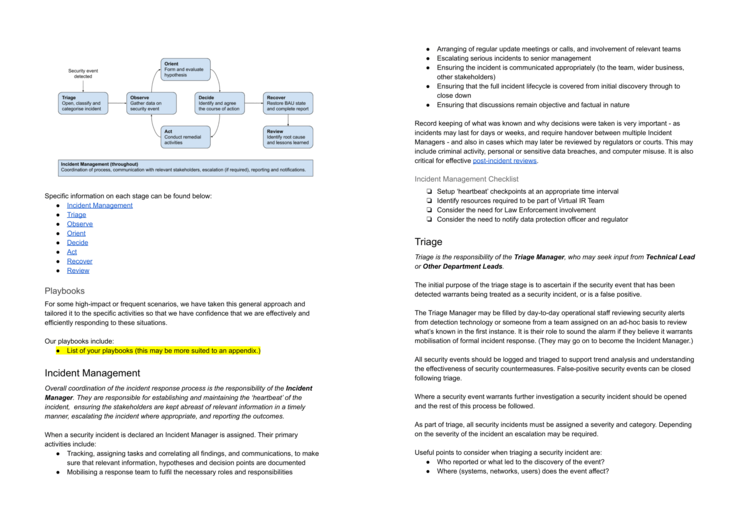
Discuss it with your team and senior management, agree this is how you'll operate:
- define who your key contacts are, and who deputises for them
- tailor the severity levels and escalation criteria
- choose the categories that you’ll assign to incidents
And then try running a few exercises to test everyone knows how it works.
Incident Response Plan Template - LG (Large)
If you need more refined, enterprise level IR plan template, you can find US consultancy Counteractive Security](https://github.com/counteractive) that delivers innovative ideas on the ends and means of modern information security.
This IR plan template was developed to help all organizations get a good start on a concise, directive, specific, flexible, and free incident response plan. Build a plan you will actually use to respond effectively, minimize cost and impact, and get back to business as soon as possible.
Download or fork this template on GitHub If you prefer to work in Microsoft Word (.docx format), download the example word version.
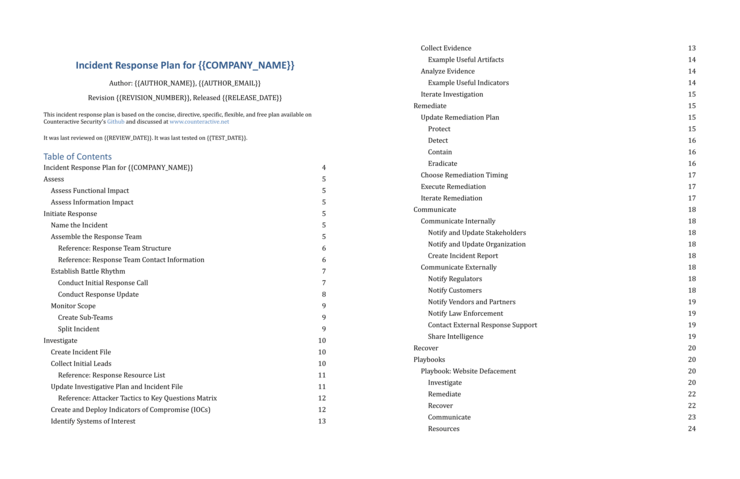
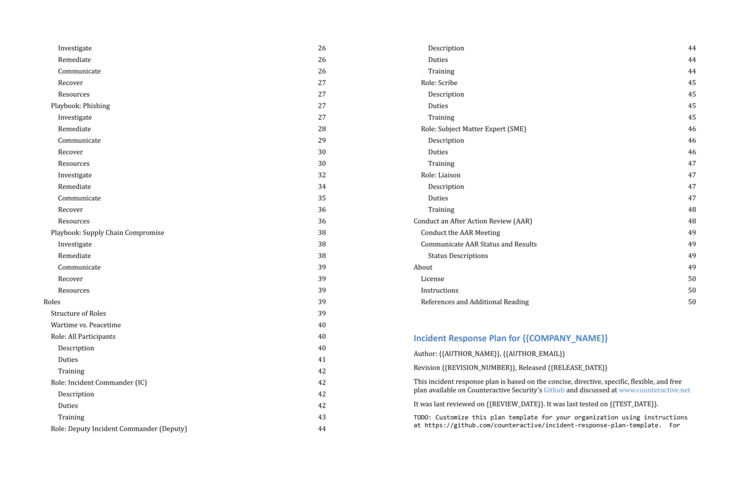
The repository contains also playbooks that capture common investigation, remediation, and communication steps for particular types of incident:
Incident handling and reporting procedures
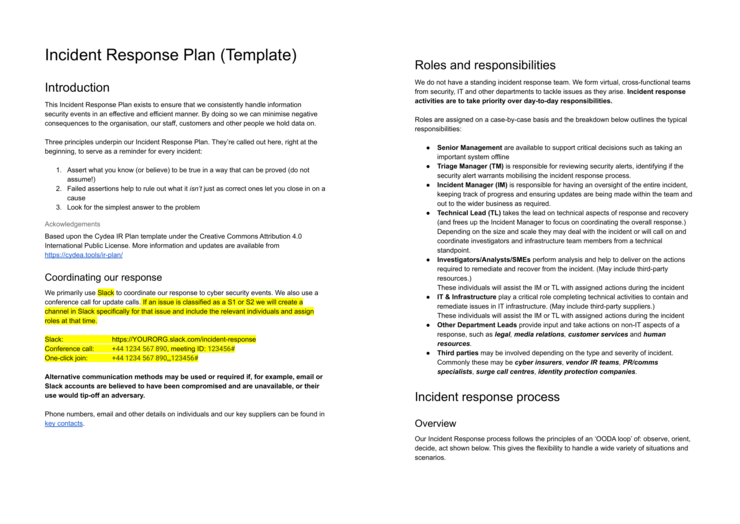
To achieve success with your IR process, your team should adopt an organized and coordinated approach to any incident regardless of the severity level. 5 response steps cover this process:
Preparation Design predetermined guidelines or plan to support your IT team. Your IR plan should include IR policies, communication guidelines, Threat Intelligence Feeds, Game Days, and your threat detection capability assessment.
Detection and Reporting In this section, you can monitor cybersecurity incidents to detect, alert, and reporting possible events.
Triage and Analysis This is where you understand the scope of the incident. You also leverage tools, systems, and technologies to detect indicators of compromise(IoC).
Containment and Eradication This stage is critical as you leverage the intel from IoC during the analysis phase to contain and rebuild the system.
Post-Incident Activity Having resolved the incident, document the process to help you manage future events.
Runbooks - Practice, Practice, Practice
When you detect an anomaly in your system, it is important to have an incident response plan that can help you restore your system to its original state. For instance, a security misconfiguration could necessitate the removal of variance and the redeployment of assets with the proper configuration. A runbook is a documented format for implementing this process.
What is a Runbook? A runbook incorporates the series of actions and steps you can take to enrich data, contain threats and send notifications automatically as part of your security operations process.
A common runbook includes:
- System configuration
- System processes
- Security and access control
- Configuration management
- Maintenance tasks
- Operational tasks
- Monitoring and alerting
- Failure and recovery process
Runbooks include data from ITIL processes like knowledge management and enhance incident management. Runbook automation through IT management software enables you to set up runbooks and automate their implementation, with humans intervening at specific points.
Runbook Automation Tools for Startups
- Rundeck - Open source automation tool for streamlining the automation of DevOps, runbook, and other IT operations tasks
- Confluence - For storing documentation and organization
- ServiceNow/Jira - Ticket tracking for managing the incident
- Slack (or other chat tools) - Real-time collaboration and communication engine
- VictorOps - Incident response and communication solution
Run Game Days
The best time to learn about fire is when you are set on fire. This is true when it comes to managing cyber incidence. Your IT Team needs to practice how to respond to security incidents. Gameday or an incident response simulation is the best way to learn. It can take hours or days depending on the time you invest in it.
A game day could range from asking your employees to click a phishing link to infecting an isolated system to stopping an event where you lose control of all data and systems and then responding to it. In the Military, this is referred to as drills or exercises.
Practicing game days can enable you:
- Align with regulatory requirements and best practices.
- Train your employees on how to respond to incidents.
- Hone problem-solving skills
- Unravel tools you can leverage to investigate, contain, eradicate, as well as recover from incidents.
- Create and maintain IR plans in the forms of playbooks, runbooks, escalation, and others.
You can read further on How to Run Game Day
Summary
A comprehensive incident response template safeguards your startup from security and data breaches, and a loss of revenue. The faster you can detect and respond to security incidents, the lower the chance those events will have an impact on your customer trust, important data, reputation, and bottom line.

![Incident Response Plan Template For Startup [SM, MD, XL]](/.netlify/images?url=_astro%2Fincident-response-plan-template.BFkeCar-.png)

![AWS Security Incident Response Plan [Practical Guide]](/uploads/aws-security-incident-response-plan.png)
